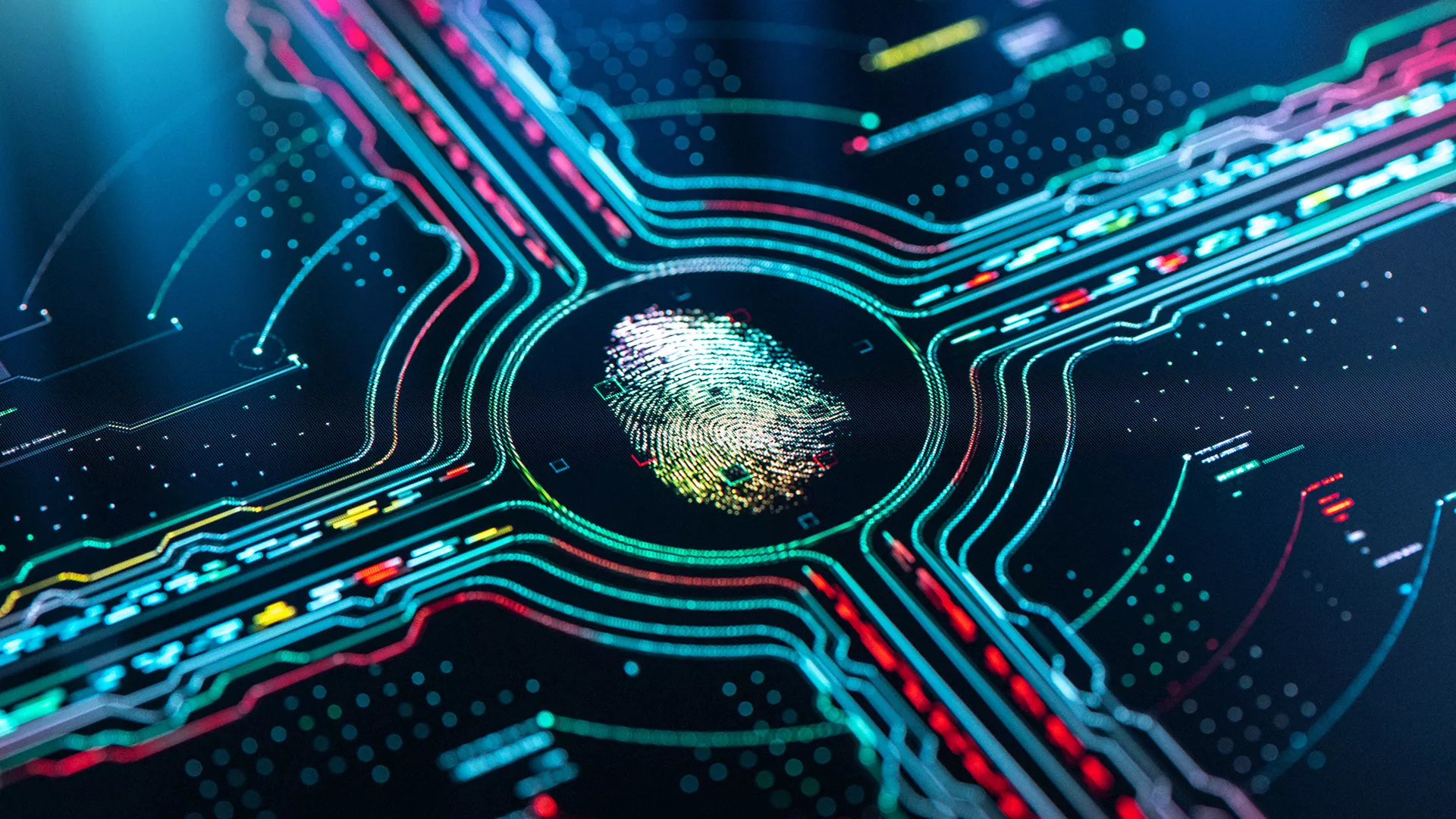
Cybersecurity solutions specialized for eGovernment use cases.
The advantages of eGovernment services are clear: it is less time-consuming for both citizens and employees, they are available 24/7, and less prone to errors.
eGovernment has significantly facilitated access to government services for both citizens and businesses. However, there is still significant room for improvement. When establishing eGovernment services, appropriate cybersecurity measures should be taken into consideration in order to ensure the data protection of users as well as the protection of government authority.
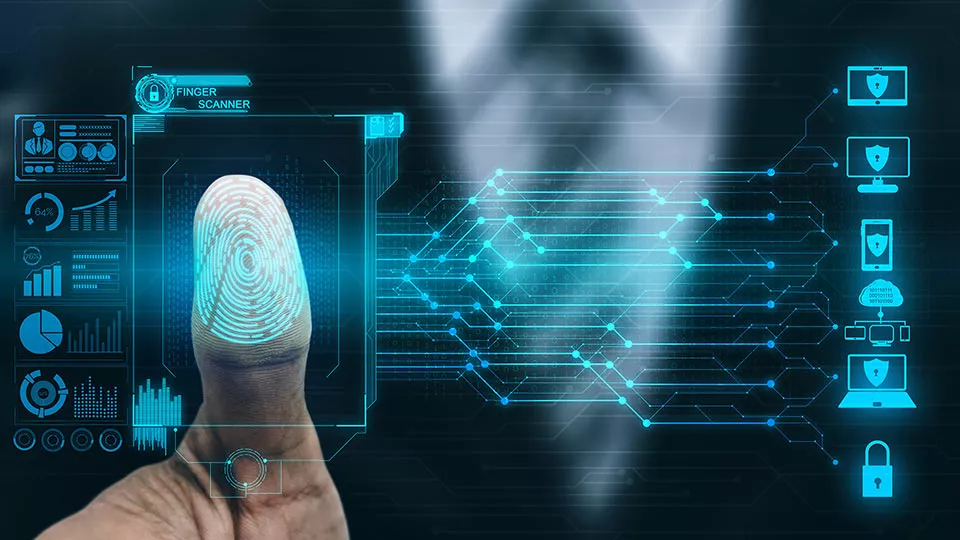
This would mean ensuring that online communication interfaces for Government-to-Citizen (G2C) and Government-to-Business (G2B) communication cannot be manipulated by hackers and, as a result, only trusted devices have access and certain documents can be uploaded.
This approach is far-reaching as many countries are supporting cybersecurity initiatives and directives that call for a security-by-design approach that is applied from outset in emerging key enabling technologies.
With secure, reliable, and trusted cybersecurity and compliance solutions, Utimaco supports the government and public sector in achieving their cybersecurity objectives.